Security Monitoring
Featured Post
See moreUpdate Your Python Version is crucial for ensuring that you have access to the latest features, performance improvements and security patches. This guide will walk you […]
Affiliate marketing has become a crucial component of many digital marketing strategies, allowing individuals and companies to earn commissions by promoting products and services. Success in […]
Affiliate marketing blog is a dynamic and ever-evolving field, with trends, strategies, and technologies constantly changing. To stay ahead of the curve and ensure success, it […]
Updates
See moreAffiliate marketing has become a crucial component of many digital marketing strategies, allowing individuals and companies to earn commissions by promoting products and services. Success in […]
Affiliate marketing blog is a dynamic and ever-evolving field, with trends, strategies, and technologies constantly changing. To stay ahead of the curve and ensure success, it […]
As we gear up to Celebrate Independence Day 4th of July, HOSTNOC is excited to announce a special Celebrate Independence Day 4th of July that will light […]
Dedicated Server
See moreCloud trends IT industry is rapidly evolving but you won’t know it if you see the market share of some of the big names in the […]
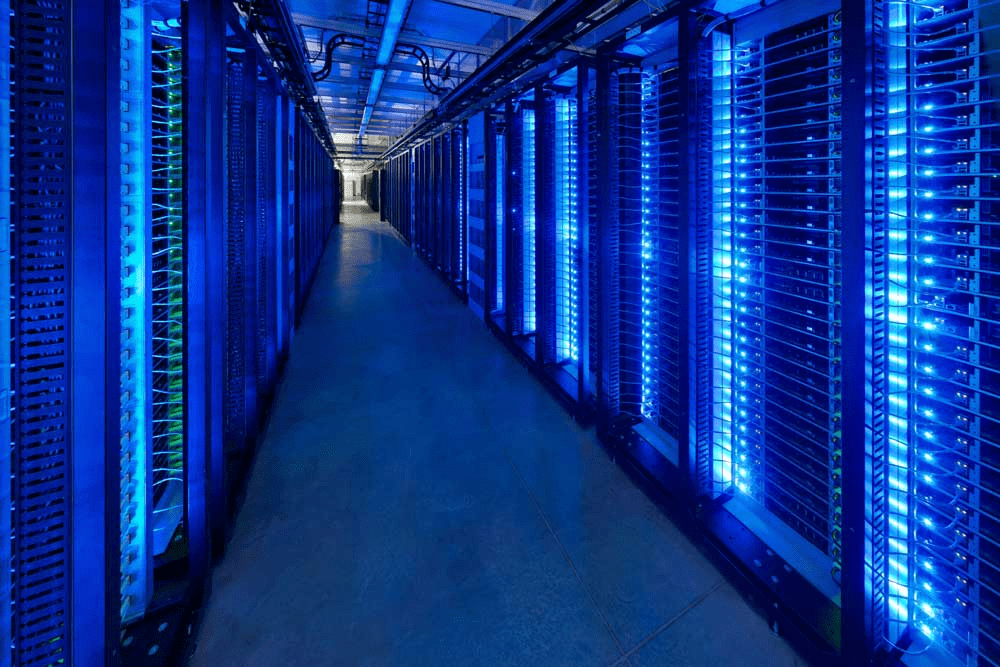
When setting up a website, choosing the right web hosting service and storage solution is crucial. While shared and virtual servers are options, a dedicated server […]
Did you know what is the biggest energy consumer in your data centers? It is your server. A major chunk of your data center energy costs […]
Wordpress
See moreYou are in a hurry and want to get some information from the internet. You search the internet and click on the link that looks more […]
After launching WordPress 5.9 a few months back, which brought much-needed improvements to the editing experience, WordPress is taking things a step further by integrating full […]
Security Monitoring
See moreIn today’s rapidly evolving digital landscape, Cloud Security computing has emerged as a transformative force, offering organizations unmatched scalability, flexibility, and cost-efficiency. However, amidst the boundless […]
You might be familiar with Software as a Service (SaaS), Platform as a Service (PaaS) and Infrastructure as a Service (IaaS) but have you ever heard […]
Did you know that 85% of all emails are spam? According to email spam statistics, 122.33 billion email messages are sent every day. In fact, the […]
Cloud Management
See moreAccording to Accenture data, Only 44% of businesses have adopted the cloud globally. This means that there are still 56% of businesses who have not adopted […]
In today’s rapidly evolving digital landscape, Cloud Security computing has emerged as a transformative force, offering organizations unmatched scalability, flexibility, and cost-efficiency. However, amidst the boundless […]
In cloud Repatriation vast majority of businesses who have jumped on the cloud bandwagon are unable to take full advantage of it. Limited control, lack of […]