Blogs

Setup Steam on a Dedicated Server: 5 Easy Steps for Gamers
September 27, 2021
7 High Paying IT Skills to Take Your Career to The Next Level In 2022
October 15, 20216 Proven Ways To Enhance Your Enterprise Data Privacy
According to data privacy statistics, the annual privacy expenditure has surpassed $1.2 million. Large-scale enterprises spend an average of $1.9 million annually on data privacy, while small businesses average of $800,000.
Most enterprises are not only seeing positive returns on their data privacy investments, but 40% of them are even getting twice as much benefit from it. In fact, 42% indicated that their private investments help them stay agile and innovate continuously.
Despite this, most businesses still struggle with emerging data privacy challenges, such as ensuring data protection for remote workers and making safe data transfer and migration possible. How can enterprises strengthen their privacy defenses to cope with emerging privacy issues? If you are looking for the answer to this question, then you are at the right place.
In this article, you will learn six ways to improve the data privacy of your enterprise.
According to data privacy statistics, the annual privacy expenditure has surpassed $1.2 million. Large-scale enterprises spend an average of $1.9 million annually on data privacy, while small businesses average of $800,000.
Most enterprises are not only seeing positive returns on their data privacy investments, but 40% of them are even getting twice as much benefit from it. In fact, 42% indicated that their private investments help them stay agile and innovate continuously.
Despite this, most businesses still struggle with emerging data privacy challenges, such as ensuring data protection for remote workers and making safe data transfer and migration possible. How can enterprises strengthen their privacy defenses to cope with emerging privacy issues? If you are looking for the answer to this question, then you are at the right place.
In this article, you will learn six ways to improve the data privacy of your enterprise.
Key Takeaways
- Data privacy is a major investment: Enterprises spend significant amounts on privacy, with large organizations averaging $1.9 million annually and small businesses around $800,000.
- Privacy investments deliver measurable value: Many organizations report strong returns, with 40% achieving double the benefits and 42% gaining greater agility and innovation capabilities.
- Asset visibility is essential: Maintaining a complete inventory of digital assets helps organizations identify, monitor, and protect sensitive data effectively.
- Understanding risk posture strengthens defenses: Regular security assessments, penetration testing, and proactive threat hunting help organizations identify vulnerabilities before attackers exploit them.
- Policies, culture, and training matter: Strong privacy policies, regulatory compliance, and a risk-aware workforce are critical for reducing data privacy risks.
- Secure data access and migration: Encryption, endpoint security, role-based access controls, and multi-factor authentication (MFA) help protect data during storage, access, and transfer.
6 Ways to Improve Enterprise Data Privacy
Here are six ways you can adopt to boost your enterprise’s data privacy.
1. Maintain an Inventory of Digital Assets
If you are serious about your enterprise data privacy, the first thing you need to do is to create and maintain an inventory of digital assets. You cannot protect something when you don’t know that it actually exists and you are the one who owns it. Invest in digital asset and inventory management tools that can offer real-time insights into all your digital assets. Ensuring visibility is critical to success when it comes to ensuring the security and privacy of data.
2. Know Your Risk Posture
The sad truth is that most businesses are unprepared to deal with remote work. The pandemic has accelerated remote work adoption, creating loopholes in your system that cybercriminals can exploit. Conduct architectural assessments and penetration testing to know your risk posture. Pandemic or not, remote work is here to stay, so your enterprise needs to prepare for it.
According to Kumar Ritesh, Founder and CEO of CYFIRMA, “To effectively reduce the number of cyber intrusions, a radical mindset shift is needed. Leaders must redefine the concept of a strong cyber posture and relegate event-based security to its rightful place—as an inferior approach to managing cyber risks and threats. A more effective approach to prevent data breaches and intrusion would be an intelligence-driven approach where a proactive hunt for threats would take centre stage.”
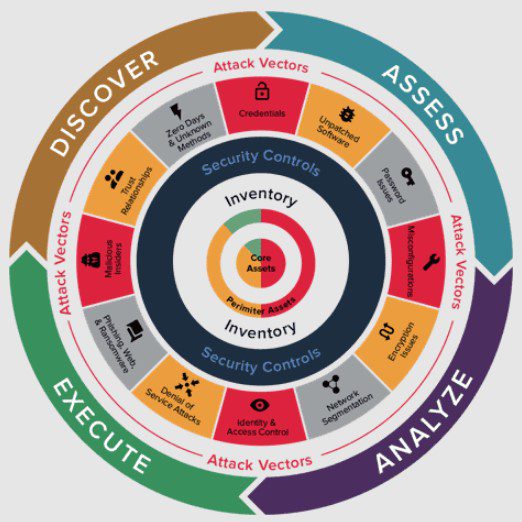
Once you understand the risk posture of your enterprise, it will assist you in dealing with new vulnerabilities in a much better way. Not only that, but it will also help you in making disruptive changes and performing large-scale redesigns in an efficient manner. You need to know how good your cybersecurity and privacy defenses are at keeping cyberattacks at bay.
3. Enforce Policies
According to Gartner’s predictions, 65% of the world’s population will be covered by modern privacy regulations by 2023. Even though your enterprise’s privacy policies will be hugely influenced by your local government data privacy laws, creating a data privacy policy and implementing it is crucial. Create a data privacy policy, manage your data securely, and prevent it from abuse. This will help you minimize the risk of potential data breaches and cybersecurity attacks.
4. Foster a Risk-Aware Culture
Most organizations treat cybersecurity and data privacy as two separate entities. With cybersecurity converging with data privacy, they need to rethink their approach. You must hire subject matter experts who know how to protect your data both from a cybersecurity and data privacy standpoint. Look for cybersecurity professionals who are ISACA’s Certified Data Privacy Solutions Engineer. These are competent and highly qualified engineers who know how to develop and implement solutions while mitigating the risks.
5. Implement Tools For Better Security Hygiene
Maintaining good security hygiene is pivotal for data privacy and security. This would only be possible if you have access to tools such as encryption, which can help you secure data both at rest and in transit. Focus on protecting your identities irrespective of the cybersecurity maturity of your organization. Next, you should invest in endpoint security, so you have clear visibility into all the nodes in your network. Make it a habit to treat personal data responsibly, irrespective of whether that data belongs to your customers, employees, or any other stakeholder.
6. Practice Caution When Accessing and Migrating Data
Most enterprises manage to protect their data when it is at rest but the real security threat emerges when they are moving or migrating their data from one place to another or when they are accessing their personal data. That is why enterprises need to be extra cautious when moving or migrating their data. Enforce role-based access so your employees only have access to the information they need to complete their work. Keep a close eye on employees who have privileged user access. Implement multi-factor authentication to add an extra layer of protection on top so that even if the hackers manage to guess your passwords, they won’t be able to access your accounts.
What steps do you take to boost data privacy in your organization? Share it with us in the comments section below.
Featured Post
7 Key Takeaways From IDC AI in Networking Report 2026
Artificial intelligence is widely expected to transform enterprise networking, but the IDC AI in Networking report 2026 reveals a more complex reality. While ambitions remain high, […]
7 Key Takeaways from the IBM X-Force 2026 Threat Intelligence Index
The IBM X-Force Threat Intelligence Index 2026 paints a stark picture of the modern cyber threat landscape, one where artificial intelligence (AI) accelerates the pace of […]
SSL Certificate Chain: A Comprehensive Guide
In the modern era of the internet, security is of utmost importance, especially when sensitive data such as passwords, credit card numbers, and personal information is […]